There is a particular kind of hype that surrounds quantum computing. It arrives in waves, usually attached to a press release from Google, IBM, or a well-funded start-up, and it tends to describe something called a “milestone” in language so breathless it is almost impossible to extract the actual meaning. What has changed? What does it do? And, most importantly, does any of it matter to the person checking their Barclays account on the Tube? The answer, in the long run, is yes. Quite significantly. Here is the quantum computing breakthrough explained, without the theatre.
What Does a Quantum Computer Actually Do Differently?
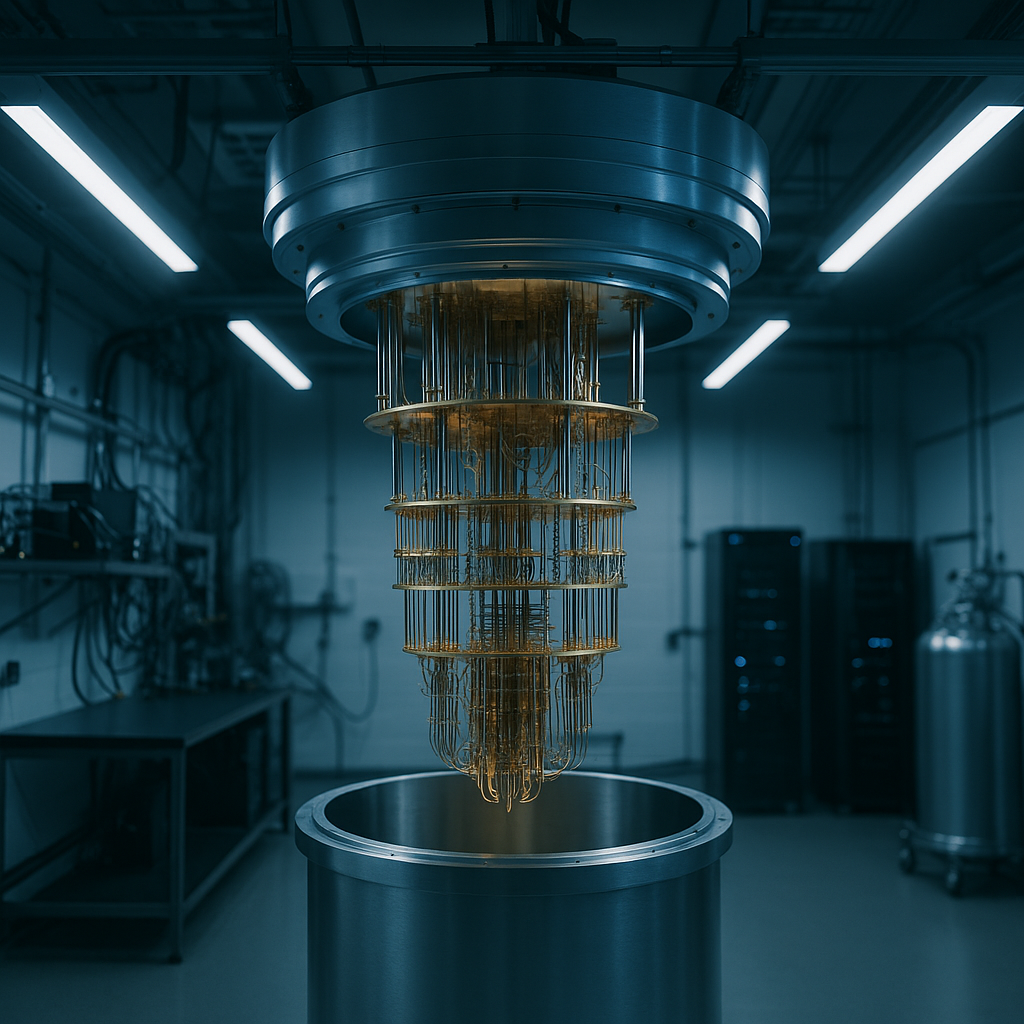
A classical computer, the sort running every smartphone, laptop, and data centre on the planet, processes information as bits. A bit is either a zero or a one. Binary. Simple. A quantum computer uses quantum bits, or qubits, which can exist in a state called superposition, essentially being zero and one simultaneously, until they are measured. This is not a metaphor or a shorthand. It is a physical property of particles at the subatomic level, and it allows quantum machines to explore vast numbers of possible solutions to a problem at the same time rather than working through them sequentially.
Add to that a second property called entanglement, where two qubits can be linked such that the state of one instantly determines the state of the other regardless of distance, and you have the makings of a machine that can tackle certain categories of problem at speeds that would take a classical supercomputer millions of years. The emphasis on certain categories is critical. Quantum computers are not universally faster. They are extraordinarily faster at specific tasks, and those tasks happen to include some of the most consequential in modern life.
What This Means for Cybersecurity in the UK
This is where the stakes become genuinely serious. The encryption underpinning almost all secure digital communication, from online banking to NHS patient records to government communications, relies on the mathematical difficulty of factoring enormous numbers. Specifically, it is extraordinarily hard for a classical computer to find the two prime numbers that multiply together to produce a given very large number. RSA encryption, used across the internet, is built on this difficulty.
A sufficiently powerful quantum computer, running an algorithm called Shor’s algorithm, could break RSA encryption in hours. We are not there yet. Current quantum machines are too error-prone and operate with too few stable qubits to threaten live encryption. But the trajectory is clear, and security professionals have been sounding the alarm for years. The National Cyber Security Centre, which is part of GCHQ, has already published guidance urging organisations to begin migrating towards post-quantum cryptography. The threat is not abstract or distant. Nation-state actors are already harvesting encrypted data today, intending to decrypt it once quantum capability reaches the necessary threshold. This is known in the intelligence community as “harvest now, decrypt later”.
The quantum computing breakthrough explained in security terms is this: the locks protecting the internet were designed without quantum keys in mind, and the window to replace them is narrowing.

Pharmaceuticals and the Drug Discovery Revolution
Here the implications are considerably more hopeful. Drug discovery is, at its core, a problem of molecular simulation. To design a drug that interacts precisely with a protein in the human body, researchers must model the quantum behaviour of electrons in those molecules. Classical computers are spectacularly bad at this. They approximate and simplify. The result is a drug development pipeline that costs billions of pounds and takes over a decade, with a high failure rate.
Quantum computers are naturally suited to modelling molecular interactions because they operate on quantum mechanical principles themselves. IBM, in collaboration with several European pharmaceutical partners, has demonstrated that even current noisy intermediate-scale quantum devices can simulate small molecules more accurately than classical methods. Companies such as Cambridge Quantum, now part of Quantinuum and headquartered in the UK, are already working with pharmaceutical firms on drug discovery pipelines that exploit this advantage.
The practical implication: conditions that have resisted effective treatment, from antibiotic-resistant infections to certain cancers to neurodegenerative diseases, may become tractable problems for quantum-assisted drug design within the next ten to fifteen years. That is not a guarantee, but it is a plausible and well-evidenced trajectory that distinguishes genuine progress from mere hype.
What Happens to Finance When Quantum Arrives
The City of London processes extraordinary volumes of financial transactions daily. Optimisation problems, including portfolio management, risk assessment, fraud detection, and derivative pricing, are computationally intensive in ways that suit quantum acceleration rather well. Banks including Barclays and HSBC have been investing in quantum research partnerships for several years, conscious that the institution which first deploys quantum optimisation at scale gains a structural advantage over every competitor still running classical algorithms.
There is also a darker edge. The same encryption vulnerability that threatens cybersecurity applies to financial systems. SWIFT transfers, card payment networks, and interbank communications all rely on cryptographic standards that quantum computing could eventually compromise. The Bank of England and the FCA are watching this space closely. Financial institutions operating in the UK will face regulatory expectations to demonstrate quantum-readiness in their security architecture, likely before the end of this decade.
Personal Privacy and What Ordinary People Should Know
For most people, the quantum computing breakthrough explained at a personal level comes down to one question: should I worry about my passwords and data today? The honest answer is not immediately, but yes, in the medium term. The passwords and two-factor authentication systems in use today are adequate against classical attack. Against a mature quantum adversary, they will not be.
The reassuring counterpoint is that the technology industry is not waiting passively. The US National Institute of Standards and Technology (NIST) finalised its first post-quantum cryptographic standards in 2024, and UK technology providers are expected to adopt these across critical infrastructure progressively. Apple has already introduced post-quantum protections in iMessage. Signal followed. The migration is slow, uneven, and largely invisible to end users, but it is happening.
According to the National Cyber Security Centre, organisations should begin their quantum-readiness assessments now rather than waiting for the threat to materialise. That advice applies to businesses of all sizes, not merely large enterprises.
The Timeline: Grounded Expectations Over Grand Predictions
The consistent failure of quantum forecasting has been overconfidence about timelines. Predictions of “quantum supremacy within five years” have been circulating since the early 2010s. What has actually happened is slower, messier, and more interesting: genuine scientific progress, significant engineering improvements in qubit stability and error correction, and an emerging commercial ecosystem. The UK government has committed over £2.5 billion to its National Quantum Strategy, recognising that quantum technology, broadly defined, represents a generational strategic and economic opportunity.
A cryptographically relevant quantum computer, one capable of breaking current encryption at scale, remains arguably ten to fifteen years away. Quantum advantage in drug discovery and financial optimisation is closer, likely within five to eight years for specific applications. The technology will not arrive all at once, like a light being switched on. It will seep into particular sectors, solving particular problems, whilst classical computing continues to handle everything else. That is both the more accurate picture and, in some respects, the more interesting one.
The quantum computing breakthrough explained honestly is this: not a single moment, but a decade of compound consequences, arriving unevenly, touching cybersecurity first and most urgently, reshaping pharmaceuticals and finance in the medium term, and eventually demanding that every institution, regulator, and citizen reconsider assumptions about digital security that have held since the 1970s. The hype is real and often tiresome. The underlying technology is also real, and the implications are worth understanding now, before the timeline compresses further.
Frequently Asked Questions
Has there actually been a quantum computing breakthrough, or is it just marketing?
There have been several genuine milestones, including Google’s 2019 claim of quantum supremacy and IBM’s progressive scaling of stable qubits. These are real engineering achievements, though none yet threatens practical encryption or delivers commercial quantum advantage at scale. The breakthroughs are incremental and real; the timelines promised by marketing teams are frequently not.
How soon could quantum computers break my bank's encryption?
Current estimates from cybersecurity experts suggest a cryptographically relevant quantum computer, capable of breaking RSA encryption used by banks, is roughly ten to fifteen years away. However, the ‘harvest now, decrypt later’ threat means sensitive data transmitted today could be at risk in the future, which is why the NCSC is urging organisations to begin migrating to post-quantum cryptography now.
What is the UK doing to prepare for quantum threats?
The UK government has committed over £2.5 billion to its National Quantum Strategy, and the National Cyber Security Centre has published specific guidance for organisations on preparing for post-quantum cryptography. UK universities, including those in Cambridge and Bristol, are among the leading research centres globally for quantum technology.
Will quantum computing help find cures for diseases?
Quantum computers are particularly well-suited to simulating molecular behaviour, which is the core challenge in drug discovery. UK-based Quantinuum is already partnering with pharmaceutical companies on this. Realistic timelines suggest meaningful quantum-assisted drug discovery could arrive within the next five to ten years for specific conditions.
Do I need to do anything now to protect my personal data from quantum threats?
For most individuals, no immediate action is required. However, using end-to-end encrypted messaging apps such as Signal, which have already adopted post-quantum protections, is a sensible precaution. Staying alert to password hygiene and enabling two-factor authentication remains the most practical personal security measure for now.
